Remove Shortcut Virus from Pen Drives, Memory Cards, USB Drives
Stop Shortcut Viruses Dead in Their Tracks! Have you ever plugged in your USB drive or memory card only to find all your files replaced by shortcuts? This frustrating issue is caused by a shortcut virus, a common malware that targets removable storage devices. Our article provides a detailed, step-by-step guide on how to remove this virus and prevent future infections, ensuring your files stay safe and accessible. From initial detection to final cleanup, we’ll show you all the tools and techniques needed to restore your pen drives, memory cards, and USB drives to full health.

- Types of shortcut viruses
- The virus turning files and folders into shortcuts
- The virus turning pen drives and memory cards into shortcuts
- What can be done if the virus attacks your PC
- Questions and answers
- Comments
Have your files and folders on a USB drive, pen drive or memory card turned into shortcuts? Is your USB drive, pen drive or memory card shown as a shortcut? Are you looking for a method to restore your data and remove the pesky shortcut virus? Is your computer infected, in spite of having an antivirus installed? Unfortunately, few antiviruses can protect you against this misfortune.
With all those nasty effects, this type of virus is relatively harmless (especially if you think of ransomware and the like) so data can be restored, and the virus removed quite easily.
Types of shortcut viruses
At the moment, the two types of shortcut viruses are the most widespread: the first type creates shortcuts instead of files and folders on a pen drive or memory card, while the other type creates shortcuts of removable drives instead of the actual pen drives, USB drives and memory cards.
Names of the most widespread viruses:
- Bundpil.Shortcu;
- Mal/Bundpil-LNK;
- Ramnit.CPL;
- Serviks.Shortcut;
- Troj/Agent-NXIMal/FakeAV-BW;
- Trojan.Generic.7206697 (B);
- Trojan.VBS.TTE (B);
- Trojan.VBS.TTE;
- VBS.Agent-35;
- VBS.Serviks;
- VBS/Autorun.EY worm;
- VBS/Autorun.worm.k virus;
- VBS/Canteix.AK;
- VBS/Worm.BH;
- W32.Exploit.CVE-2010_2568-1;
- W32.Trojan.Starter-2;
- W32/Sality.AB.2;
- Win32/Ramnit.A virus;
- Worm:VBS/Cantix.A;
The virus turning files and folders into shortcuts
This virus duplicates your files and folders, then hides and replaces them. It is a combination of a Trojan and a worm. The danger is that you start a virus every time when you want to open your file or folder. When you start a virus, it multiplies itself and infects more and more files, and often installs more malware that can steal data on your passwords and credit cards stored on your PC.
The virus turning pen drives and memory cards into shortcuts
This is a thoroughbred Trojan that hides all removable drives connected to the computer and replaces them with shortcuts for these devices. Every time you click on the shortcut, you start the virus again and again, so it starts looking for any financial data on your PC, and sends it to its creators.
| Virus Type | Description | Spread Method | Removal Methods |
|---|---|---|---|
| Shortcut Virus | Converts files and folders into shortcuts, hiding the original files. | Flash drives, external hard drives, files downloaded from the Internet. | Using antivirus software, command line to remove shortcuts. |
| Trojan Virus | Disguises itself as a useful file or program but is harmful to the system. | Downloads from the Internet, malicious programs, and email attachments. | System scan with antivirus, manually removing harmful files or through antivirus. |
| Worm Virus | Self-spreading virus that quickly infects other files and folders. | Email, networks, removable media. | Using powerful antivirus, removing infected files, and system reboot. |
| File Infector | Infects executable files and turns them into shortcuts or corrupts them. | Downloading infected files or programs, USB devices. | Antivirus scan, removing corrupted files. |
What can be done if the virus attacks your PC
Unfortunately, few antiviruses can recognize the threat in time and protect your PC from infestation. That is why the best protection is to disable autorun option for removable devices and avoid clicking on file, folder or disk shortcuts. Be attentive and don’t click on the shortcuts which you didn’t create. Instead of the usual double-click to open the drive, right-click on it and select Open in new window.
Method 1. Recover data removed by the virus
To restore effectively the data removed by this type of virus, use Hetman Partition Recovery. It uses low-level functions in working with the disk, so it can bypass the virus blocking and read all of your files.
Download and install the program, then analyze the infected pen drive or memory card. Restore the information before cleaning the drive from the virus. The most reliable method is to clean the pen drive with the command DiskPart, which will remove all data.
Method 2. Delete the virus from the memory card or USB drive
After recovering data from the pen drive, you can clean it entirely with the help of diskpart. Removing all files and formatting the device may still miss the virus hiding in the boot sector, partition table or unallocated area of the drive. Watch the video to see how to clean a pen drive properly.
Method 3. Remove the virus from the pen drive with the Command Prompt
This method cannot clean your pen drive from all kinds of viruses for sure, but it can help you to get rid of the shortcut virus. You don’t have to download and install any third-party utilities – all the work can be done with this Windows-integrated tool.
-
Right-click on the Start menu and run the Command Prompt as Administrator.
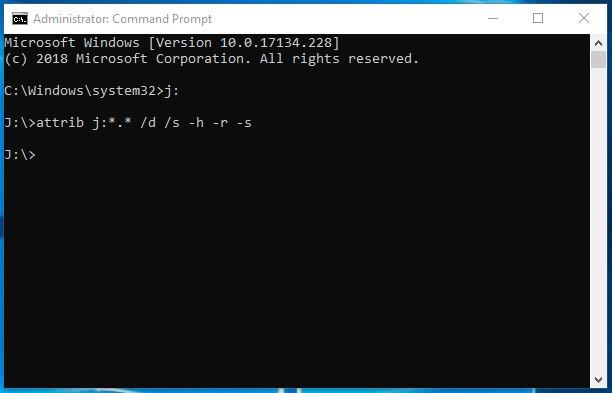
-
Enter the command j: and press Enter (where j: is the letter of the USB drive infected by a virus).
j: -
Enter the command: attrib j:*.* /d /s -h -r –s and press Enter:
attrib f:*.* /d /s -h -r –s- –h: shows all hidden files on the flash drive;
- –r: disables the read-only setting;
- –s: disables the system mark from all files.
Method 4. Delete the virus from your PC
The easiest and most reliable way to clean the computer from the virus is to completely reinstall Windows, with removing the system partition.
However, if you are a power user, here’s one thing you can try:
-
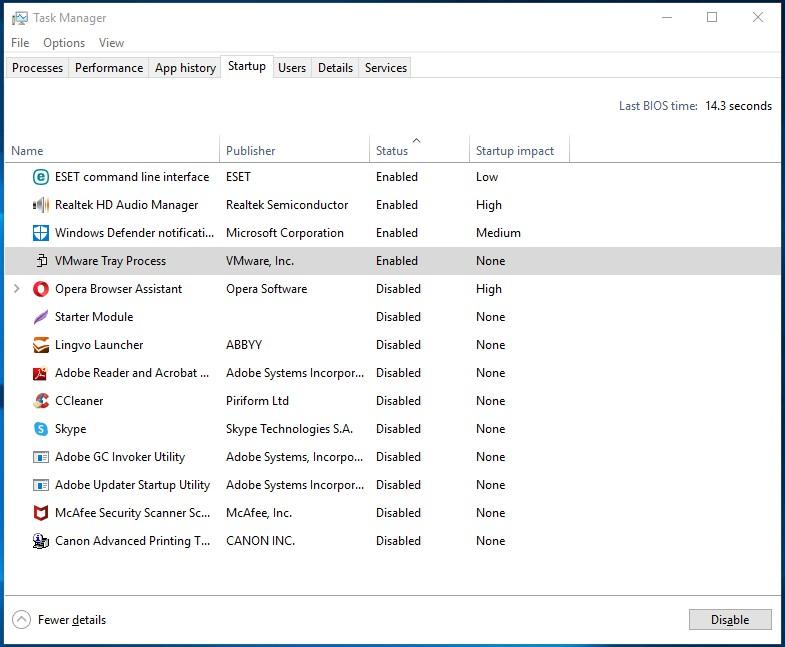
Modify the Windows registry to prevent the virus from auto-starting. Press the key shortcut Win + R, in the window that appear, type regedit and press Enter. Go to HKEY_CURRENT_USER / Software / Microsoft / Windows / CurrentVersion / Run.
HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run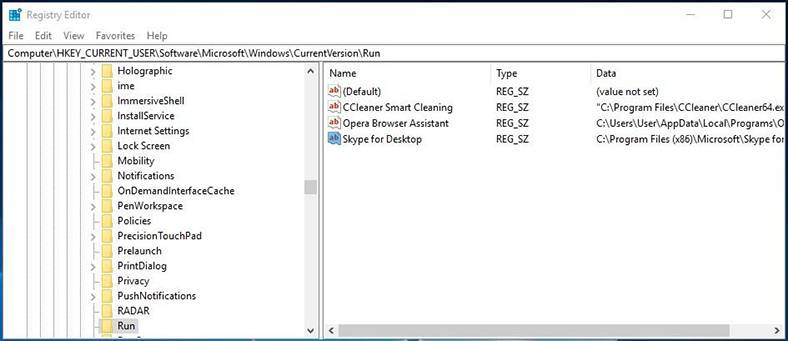
View all keys located there. If you see an unusual name or location of a program, remove the entry. Often viruses are hiding under automatically generated names, such as sfdWQD234dcfF. Any keys starting VBS, INI, LINK or EXE files are potentially dangerous. However, you are the person to know for sure what programs are installed on your computer and are supposed to start with Windows, so it’s up to you to decide if a certain key has to be removed. To remove a key, select it by left click and press Del.
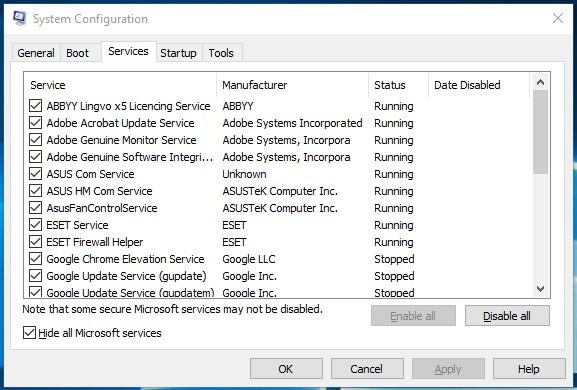
-
Disable the virus auto-start in Windows Services. Press the key shortcut Win + R, in the window that appears, type msconfig and press Enter. In the window that opens, jump to the tab Services. View them and disable all that seem to be suspicious.
-
Disable the apps that are started automatically via Task Manager (For Windows 8 and older) Press Ctrl + Shift + Esc and go to the tab Startup. To prevent a suspicious app from starting, right-click on it and select Disable.