Windows Firewall: How to Block Internet Access and Traffic
Unlock the Power of Windows Firewall! Want to control which applications can access the internet or restrict inbound and outbound traffic on your Windows PC? In this article, we’ll show you how to master Windows Firewall and effectively block internet access and traffic. Whether you’re concerned about security or want to optimize your network performance, Windows Firewall offers powerful features to help you achieve your goals. From blocking specific applications to configuring custom rules, we’ll cover everything you need to know to take control of your network traffic with Windows Firewall. Watch now and learn how to safeguard your system and data from unauthorized access!
- Step 1. Create a Widows Firewall rule
- Step 2. Test the block effectiveness
- Questions and answers
- Comments
Why would you need it? Blocking inbound traffic allows to disable unwanted software updates and annoying advertising or save your precious megabytes. Blocking outbound traffic can prevent leaks of confidential information. Blocking is also good if you want to secure your child from watching unwanted content or spending too much time playing online games.
| Parameter | Description |
|---|---|
| Name | Windows Firewall |
| Purpose | Protects the computer from unauthorized access and network threats. |
| Main Features |
– Filtering incoming and outgoing traffic – Creating and managing rules for applications and ports – Notifications about blocked connections |
| Operating Systems | Windows XP, Vista, 7, 8, 10, 11 |
| Protection Levels | Home Network, Work Network, Public Network |
| Ease of Use | Intuitive interface, configuration through “Control Panel” |
| Additional Features |
– Ability to enable/disable for individual networks – Security log to monitor blocked connections – Integration support with Windows Defender |
| Configuration | Option for manual or automatic rule setup |
| License | Free, built into the Windows operating system |
| Limitations | Does not provide antivirus protection, focused only on network traffic management |
We will have a look at how firewall works in Windows 10, but this method will also work in Windows 8 or 7.

Windows Firewall: Blocking Internet Access for an App (Outbound and Inbound Traffic) 🌐⛔💻
Step 1. Create a Widows Firewall rule
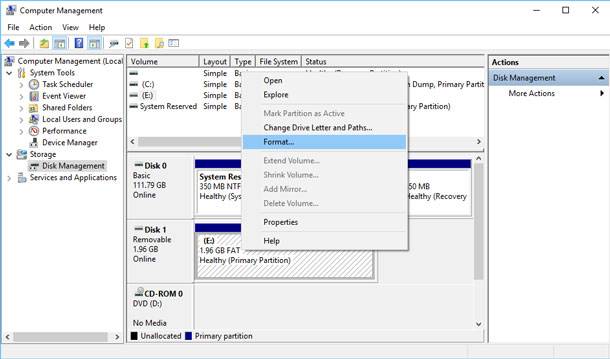
To begin with, you should start the firewall extended interface. To do it, go to Control Panel, switch to large icons mode, and click on Windows Defender Firewall.
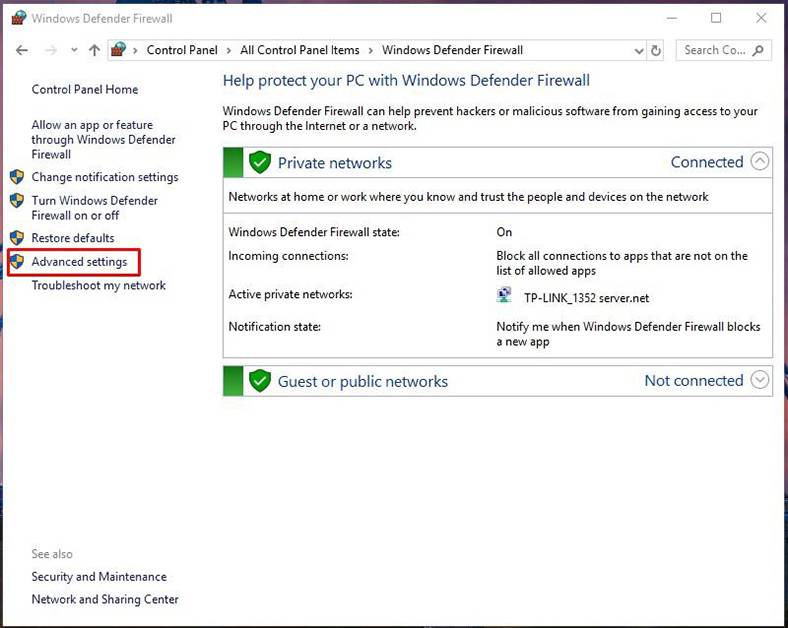
The firewall extended interface (which you can access by clicking on Advanced settings link on the left) has a lot of settings. Make all changes very attentively, and do exactly what this tutorial tells you. If you set certain things wrong, it will result in lots of problems in the work of your computer.
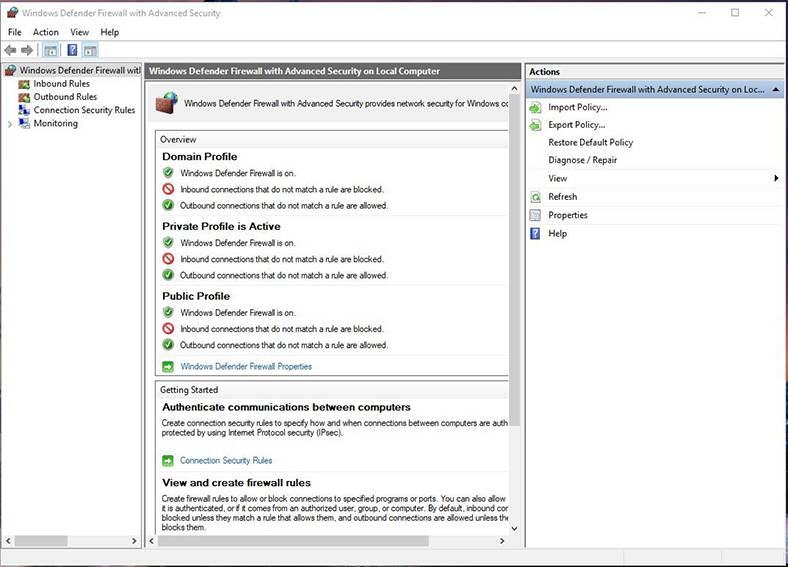
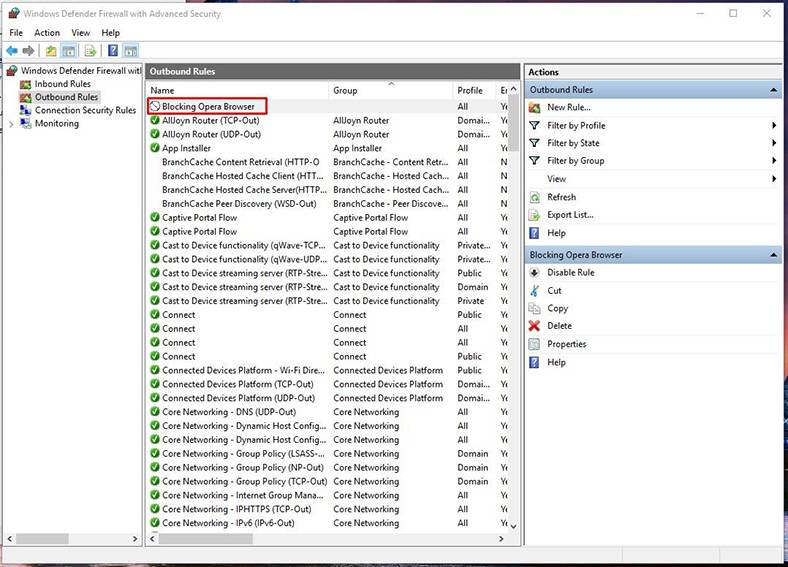
In the left navigation pane, select Outbound Rules. The system will show all rules created before – and don’t be surprised to see dozens of entries created by Windows.
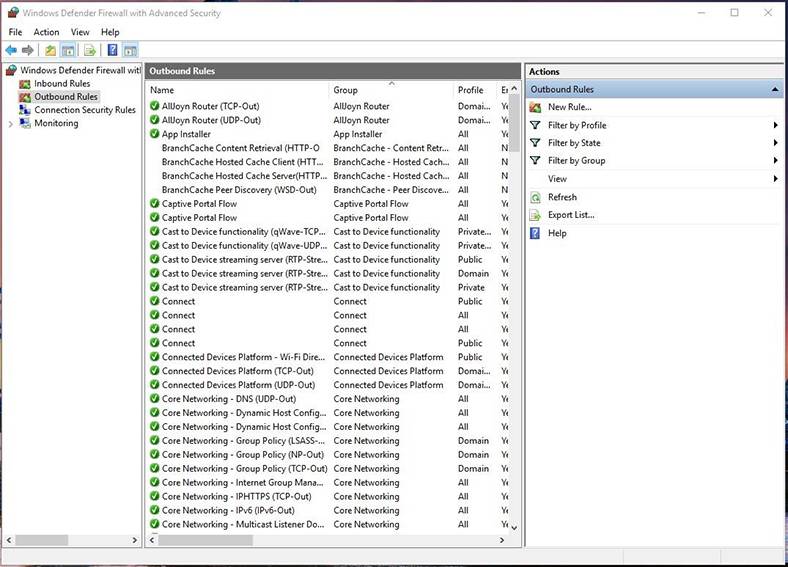
In the right pane, click New Rule….
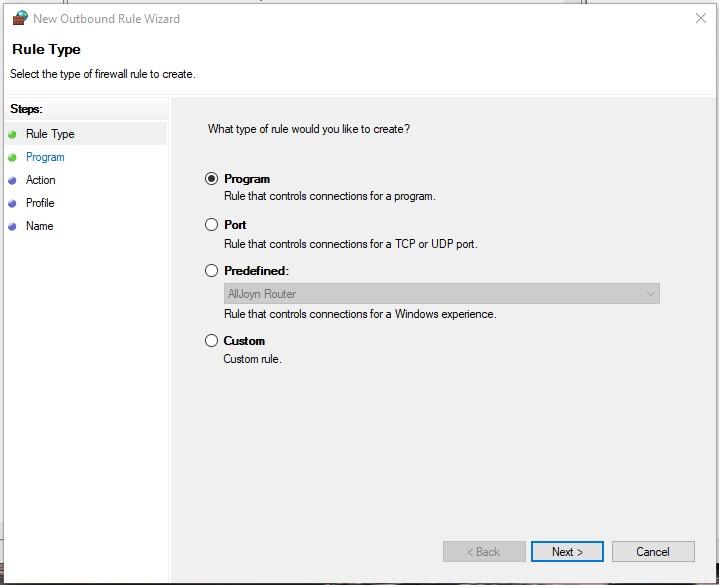
By default, you are suggested to create a rule for a program, so confirm your choice by clicking Next.
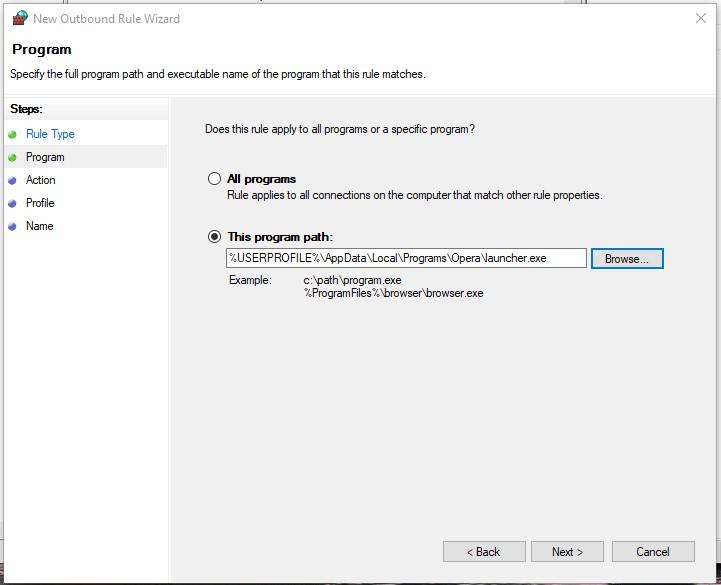
The next step is to show the path to the executable file of the program to block it.
With the example of Opera browser, we’ll see how Internet connection can be blocked. You can either enter the path to the .exe file manually or use the Browse button.
If you choose the second option, the system will automatically replace a part of the path by the environment variable.
In our case, the file address is:
C:\Users\User\AppData\Local\Programs\Opera
An important note: For a number of reasons, environment variables may be determined incorrectly by the system. If you see that a blocking rule doesn’t work properly, edit the rule by pasting the full path to the file into the input field.
Another important note: In most cases, blocking the executable file of a program is enough to restrict its Internet access. However, this approach may not work with online games. For example, if you want to block access to Minecraft game servers, you should block the corresponding Java application (executable file Javaw.exe), as the game connects to the Internet via Java.
Confirm the choice of file by clicking Next.
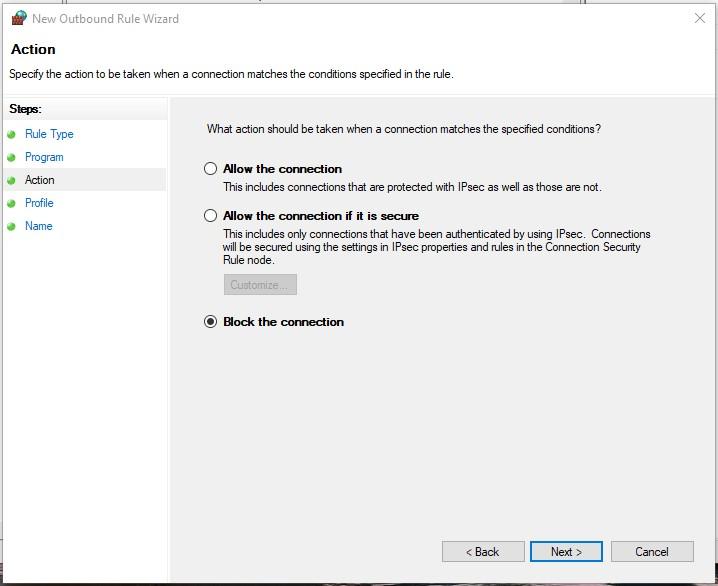
At the next stage, confirm the choice Block the connection by clicking Next.
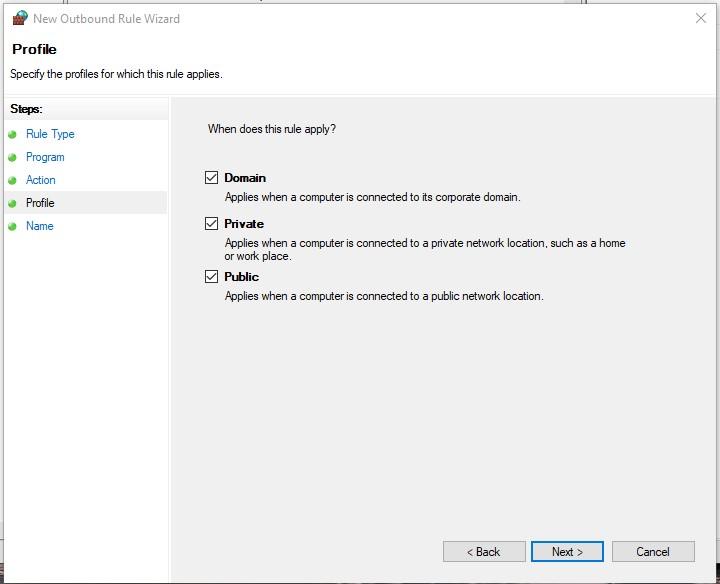
Your next step is to choose when the rule should apply (by default, all elements are checked). They determine if the rule applies depending whether the computer is connected to a network which you define as public or private.
An important note: If you choose Private and uncheck Public, it means that the program will have access to resources of the local network, but it will not have access to the Internet.
Let’s suppose you use a laptop at home (in a network you define as private), at work (in a domain network) and at a cafe (in a network you define as public). If you want the rule to apply at the cafe, at work and at home, select all the three options. If you want it to apply only in one of the three cases, select the corresponding option.
If you have doubts, just leave all blocking options enabled by default. Confirm the choice by clicking Next.
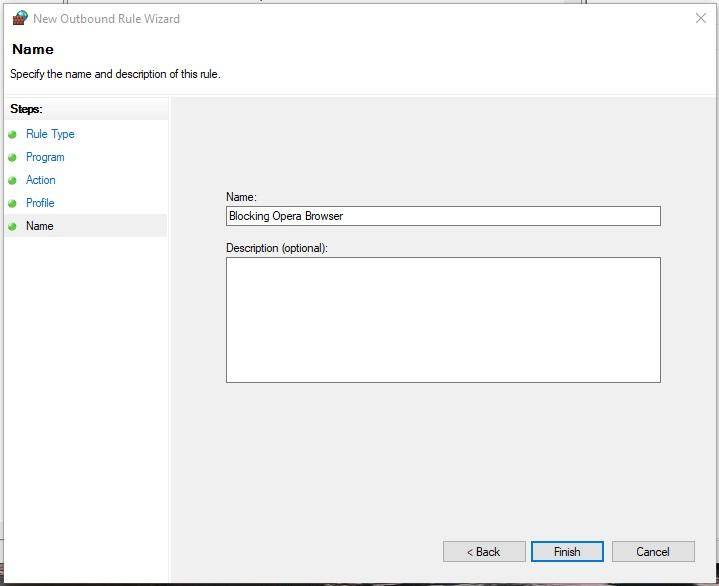
The last step is to give this rule a name. Think about a name that makes sense so that you will be able to find it easily later. At this point, you can also describe this rule so you will be able to remember why you created it - after some time. Windows creates a lot of firewall rules automatically, and all of them have quite fancy names.
To make your rule stand out, name it Blocking Opera Browser. Close the wizard by clicking Finish.
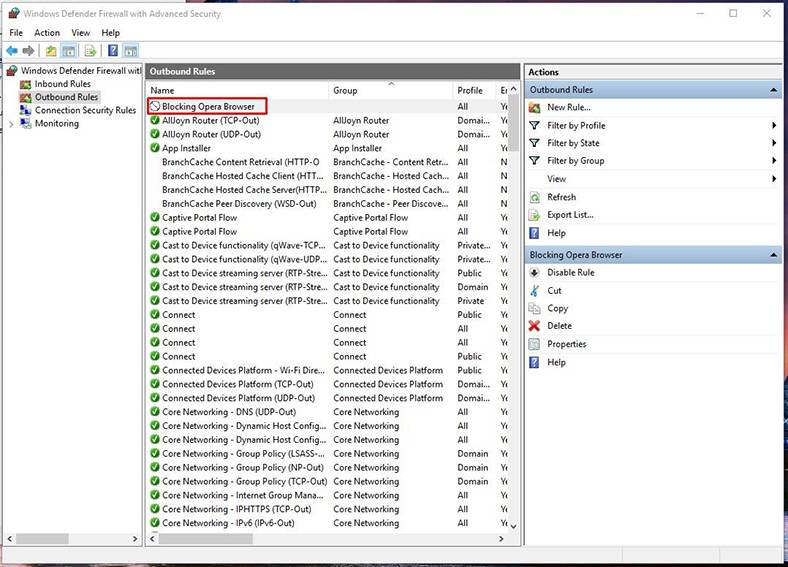
Now there is a new item on the outbound rules list. You can double-click on it to edit it. For example, you can specify the users for whom this rule will apply or not, or decide that only a certain protocol should be blocked - TCP, or other.
Step 2. Test the block effectiveness
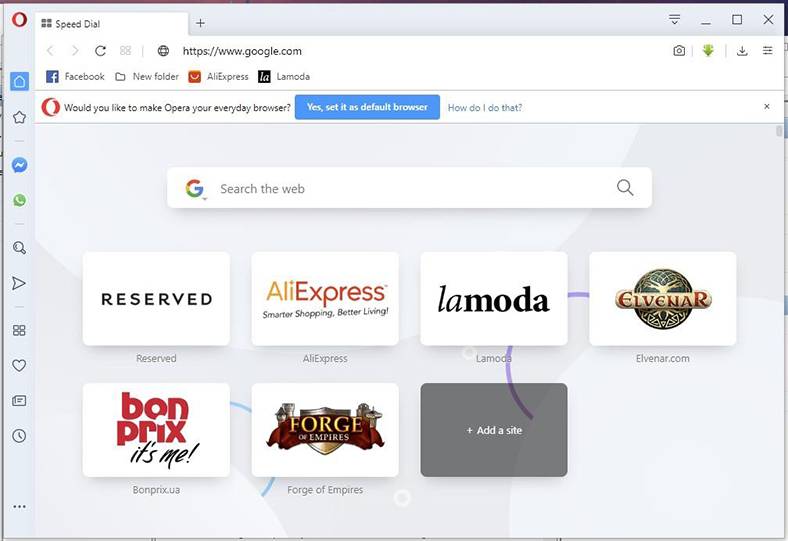
Blocking will start as soon as you create the rule so you don’t have to log off or restart. Start Opera and go to the website https://www.google.com, to make sure the connection is blocked.
If you need to disable the blocking, you will have to return to Windows Firewall advanced settings, left-click on the rule to select it and then disable or delete it. Use the corresponding items in the right pane of the Firewall to do it.