Remote Data Wipe: A Comprehensive Tutorial on Its Essentials
Explore the essential guide to understanding what’s in remote data wipe with this comprehensive tutorial. If you’re curious about the functionality of remote data wipe or need insights into its components, you’re in the right place. We provide expert solutions and explanations to help you grasp the essentials of remote data wipe effortlessly. Learn critical steps and gain insights into ensuring the safety of your valuable data through remote wiping.

Today’s gadgets are infinitely more complex than those early computers. Unlike old computers, today’s smartphones, tablets and transformers have nearly 100% connectivity, being part of the global network almost all the time.
With high technology spreading to every household and city legends demystified, there are now less concerns about a malicious person deleting the data. There are more people concerned with their personal information getting in the hands of a stranger should their mobile device get lost or stolen. So today everyone can be a hacker wiping their mobile device clean with a push of a button miles away.
- Erasing User Data Remotely: BlackBerry
- Remote Data Wipe: Android
- Recovering Erased Data
- Remote Data Wipe and Windows
- Conclusion
- Questions and answers
- Comments

How to Clean Your Android Smartphone or Tablet PC from Unnecessary Files and Apps 📱❌📝
Erasing User Data Remotely: BlackBerry
Historically, BlackBerry was the first platform offering its users (mostly corporate) the ability to erase information from their phones if the device got lost or stolen. Information could be wiped if the device falls in the wrong hands and the new “owner” entered the PIN code incorrectly several times in a row. In addition, the data could be erased by the command from a remote server. Being parts of BlackBerry’s overall security strategy, these measures were partly accountable for the BlackBerry being the first (and only) mobile device the US president was allowed to carry.
Today, BlackBerry is not all that popular. However, its competitors learned. Today, Android offers means to destroy user data remotely over the Internet with a push of a button. Let’s see how this looks like.
Remote Data Wipe: Android
Android. A free, open, expandable and highly customizable platform with little or no attention spent on data security. With rare exceptions (e.g. some Samsung devices), information stored in Android devices is not encrypted or otherwise protected, and can be obtained from the device easily once it gets into wrong hands.

Factory Reset or Hard Reset Your Android Phone: Samsung, Xiaomi, LG, Meizu, Huawei, HTC
So what are the options if your phone grows legs? Before August 2013 you could do nothing (unless you used a third-party app, that is). Things have changed when Google released Android Device Manager, an extension of Google Account allowing you to manage all Android devices registered in your account.
In Android Device Manager, you can map the location of your device on Google Maps, ring your phone even if it has a new SIM card, lock it with a password or erase user data by performing a full system reset.
These features are not a given. You have to activate them before your phone or tablet goes missing by turning the feature on and responding to the request sent to your mobile device. After you’ve done that, you are protected.
Now, if your mobile device gets lost or stolen, you can map the device on Google Maps, Ring your phone, Lock it, or Erase its content. In this article, we are more interested in how Erase works rather than the rest of it.
In Android, remote data wipe is not a 100 per cent secure. Granted, user data stored in the phone’s memory gets lost rather reliably (at least there is no easy way for an ordinary computer user to recover that data). On Android 2.3+ devices, the command also erases the content of the SD card, if installed.
However, when it comes to data stored on an SD card, there are quite a few limitations listed in Android documentation.
Namely:
SD card wipe is not activated on Android devices running Android 2.2 and earlier;
SD card wiping is not available on some devices (e.g. Motorola Xoom, Galaxy S4);
If more than one SD card is installed, only the primary card is wiped;
The wipe is performed with fast erase and not a secure erase, which makes the data susceptible to routine recovery;
Finally, read-only SD cards cannot be wiped.
Recovering Erased Data
So what happens if you get your device back after erasing its data? The internal storage is pretty much clean at this stage, and there is no easy way of getting the data back. (There might be no way to get it back physically, too.)

How To Recover Deleted Data From Android Smartphone: photos, contacts, aps 💥 🥇 ⚕️
However, any data removed from the SD card can still be recovered because Android performs a fast erase instead of using a secure method.
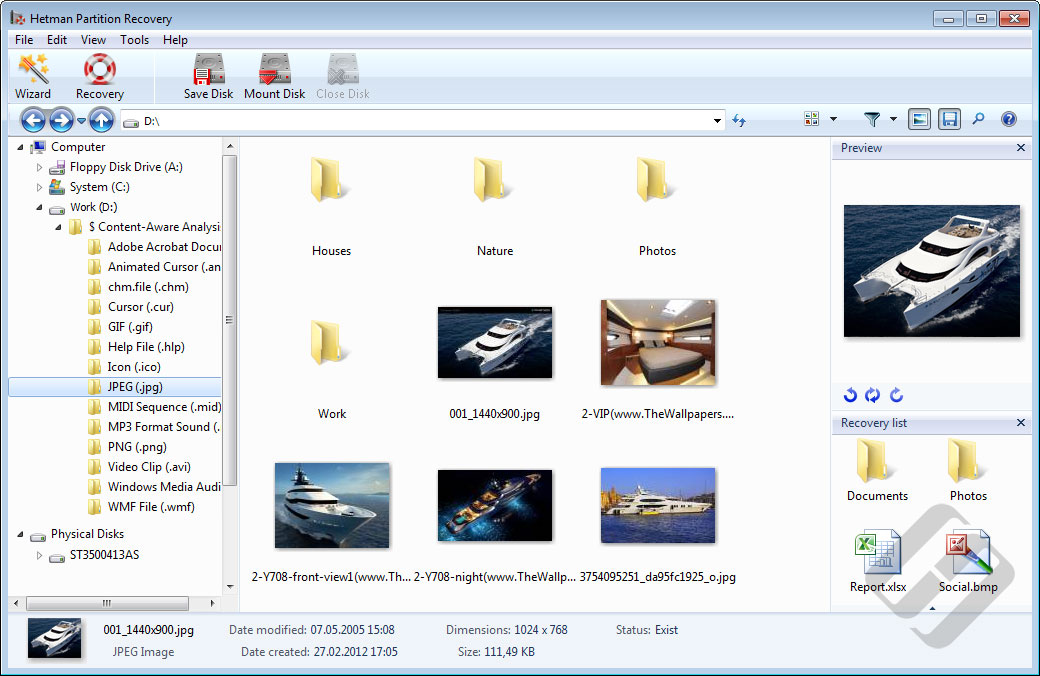
To recover information erased from the SD card, you’ll need a data recovery tool such as Hetman Partition Recovery. Make sure to take the SD card out and connect it to your PC by insert it to a card reader. Launch the program and choose the SD card from the list of available devices. Run the recovery process, and you’ll see the list of deleted files.
But what about the data stored in the device memory? This information is gone. However, you can still recover it from the cloud backup if you ever created one (you should). Configuration and management of backup copies goes beyond the scope of this article, but we strongly recommend exploring this opportunity and using this functionality on a regular basis.
Remote Data Wipe and Windows
In the Windows world, remote data wipe has long been the privilege of malware, viruses and Trojans. However, end-user solutions allowing to remotely wipe information off a laptop or desktop PC do exist.

How to Delete Files Without the Opportunity to Restore Them – Software Encryption 📁🚫⚕️
Windows is a much more complex system compared to Android, and much larger storage capacities are involved. As a result, performing a secure data wipe remotely is not that easy. Generally speaking, the only truly secure way to destroy information on a laptop is by using a model equipped with an encrypting disk controller. Destroying the decryption key only takes a brief moment while rendering the entire device effectively unreadable. What’s best, this can be performed while Windows is still running, without requiring a reboot.
If the disk was not using an encrypting controller, another option would be setting up an encrypted volume (such as TrueCrypt) and making it dismantle automatically every time the computer sleeps, shuts down or sits idle for a certain period of time. Without the encryption key, getting access to information stored on that volume would not be possible.
So let’s have a look on how modern mobile devices running Windows handle remote data destruction.
Let’s take, for example, the latest and newest transformer, Lenovo Helix. This model is equipped with an SSD drive, but has no pre-installed tool to allow remote data wipe. If being able to erase user data remotely is what you’re after, Lenovo offers LANDesk Management Suite which can be purchased separately. This toolkit contains Lenovo Mobility, a tool that can be configured to set up remote data wipe. Bear in mind that such configuration must be performed before the computer goes missing; otherwise it’s too late.
Deleting information from Lenovo Helix is a much easier task when having physical access to the device. Lenovo Helix carries an SSD drive; different models may be supplied with regular and encrypting SSD controllers. Lenovo provides a tool to securely destroy information called Lenovo Secure Data Disposal. The user must download the tool and launch it manually. The tool will reliably destroy information, but can take several hours to complete.
It’s important to note that SSD drives can be instantly wiped with a simple Quick Format operation. If certain conditions are observed (the formatting is performed in Windows 7 or Windows 8, and the new volume is NTFS), then the disk’s built-in garbage collector will begin physically erasing blocks of data immediately after receiving the TRIM command. While the actual wipe will take some unpredictable time, any attempt to read information from a quick-formatted disk will return zeroes regardless of whether or not the data is still physically available. That’s how the combination of TRIM and SSD garbage collection works in most models. If you are interested on how SSD drives handle deleted information and what can be done to recover it, read our previous articles “Recovering Information from SSD Drives: Myths and Reality” and “Securely Destroying Information: The Issue of Solid-State Drives”.
Cleaning a disk equipped with an encrypting controller is generally a much simpler, faster and more reliable endeavor. If an encrypting controller is in use, it is enough to destroy the decryption key to render the complete content of the device effectively inaccessible. Lenovo Helix users can enable this feature via the ThinkPad Setup Menu Extension Utility. Alternatively, this feature is available via the ThinkPad Setup application. Of course, it’ll only work in models equipped with drives featuring encrypting controllers.
Conclusion
The ability to wipe user data from mobile phones and tablets is a regular feature of Android devices since August 2013. For Windows users, there is no easy answer. With huge variety in hardware, fast and secure remote data wipe may be or may not be possible. Either way, third-party software is required to perform the task.