Restore Protected NTFS Files: Recovery Tips
Recovering protected and encrypted NTFS files can be a daunting task, but it’s not impossible! In this article, we delve into the complexity of this challenge and unveil effective strategies for success. Whether your files are safeguarded with passwords or encryption, we’ve got you covered. Learn how to decipher the complexity and recover your valuable data!

This is Part I of the article “Recovering Compressed, Protected and Encrypted NTFS Files” covering NTFS access control rights and on-the-fly encryption. The second part will discuss the ability to recover NTFS compressed files.
- NTFS Access Control Rights
- NTFS File Encryption
- Recovering NTFS Encrypted Files
- Tools and Limitations
- Questions and answers
- Comments
NTFS Access Control Rights
NTFS introduced a new feature allowing the operating system to control who can and who cannot access a given file, folder or disk. The feature uses file system attribute known as ACL (Access Control List) to allow or disallow certain activities such as the ability to read, write or create files, list the content of a folder, or change file permissions.
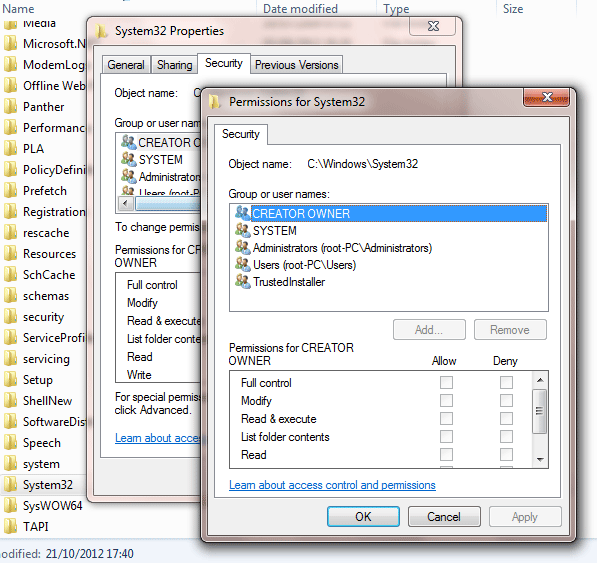
As many files belong to different users, including the operating system itself, strict obedience to permissions set in the access control list would restrict system administrators from being able to recover users’ files, or at least slow down the process significantly. For this reason, pretty much data recovery algorithm will ignore file access permissions by reading the disk directly, bypassing the high-level API of the file system. Effectively, NTFS access control lists are nothing to worry about when recovering information – if you have administrative rights on a given PC.
NTFS File Encryption
NTFS file encryption adds an extra layer of security. Not to be mistaken with access control rights, the encryption will actually alter the contents of the files, encrypting them with a strong encryption key derived from the user’s Windows account password.
NTFS encryption works differently compared to access control rights management. It is impossible and plain inefficient to recover such files in the direct disk access mode, even if their details are available in the MFT (Master File Table). While you can still read files “locked” with ACL attributes on another PC by simply changing or bypassing the attributes, encrypted files cannot be accessed as easily even if you have low-level access to the original disk. If you don’t know the exact password, you won’t be able to decrypt the content of encrypted files, which makes them effectively unusable. Note, however, that this only applies to situations when you are trying to recover somebody else’s files without knowing the original Windows account password. If you do know the password, you can read the encrypted files even on another PC.

How to Encrypt a USB Disk with BitLocker, Unlocking with Password or Recovery Key 🔐💻⚕️
Recovering NTFS Encrypted Files
NTFS-encrypted files must be accessed via Windows API’s, which basically means no low-level disk access in raw mode. The inability of data recovery tools to use raw disk access puts numerous restrictions on recoverability of NTFS-encrypted files. However, the recovery is still possible if you choose the right tool.
Tools and Limitations
Some of the more advanced NTFS recovery tools will correctly detect and process encrypted files – provided that the files were encrypted by the same Windows account you are logged in at the time of recovery, or at least if you know the original account password. The “how-to” tutorial on accessing NTFS-encrypted files from another PC is out of the scope of this article, so let’s just put a note that it is possible.
The recovery of NTFS-encrypted files carries certain restrictions and limitations, making the ability of a given tool to recover a given file under given circumstances a case-by-case issue.
NTFS volume recovery tools such as Hetman NTFS Recovery will be able to detect and recover encrypted files under certain conditions. Knowing the right password is essential, but it’s not enough. Hetman Partition Recovery will need to use high-level Windows API’s to read encrypted files (as opposed to using direct disk access in raw mode). Thus the recovery of encrypted files will depend on whether or not Windows disk API is still able to read the file. For example, undeleting encrypted files located on a healthy disk is no different to undeleting any other type of file. Recovering NTFS-encrypted files from formatted NTFS disks is iffy, but generally still possible. If the file system is badly damaged, the chances of correctly recovering NTFS-encrypted files are much lower than those for non-encrypted ones. However, it’s always worth a try to see if your files in your situation are actually recoverable.
| Feature | Hetman Partition Recovery | Hetman Uneraser | Hetman Office Recovery |
|---|---|---|---|
| File System Support | FAT/exFAT, NTFS/ReFS, APFS/HFS+, Ext2/3/4/ReiserFS, XFS/UFS/ZFS/Btrfs/VMFS/HikvisionFS | FAT/exFAT, NTFS/ReFS, APFS/HFS+ | FAT/exFAT, NTFS/ReFS, APFS/HFS+ |
| Recovery Types | Recovery of lost and deleted partitions, as well as data from damaged partitions | Data recovery from damaged or formatted partitions | Recovery of damaged or lost Microsoft Office documents (Word, Excel, PowerPoint) |
| Recovery after Formatting | Yes | Yes | Yes |
| Recovery from Damaged Disks | Yes | No | No |
| Operating System Support | Windows, Linux, macOS | Windows, Linux, macOS | Windows, Linux, macOS |
| Virtual Machine Support | Supports virtual machines | Does not support | Does not support |
| Preview Mode | Preview of recovered data available | Preview of recovered data available | Preview of recovered documents available |
| Document Recovery from Various Formats | Supports recovery of Office documents (Word, Excel, PowerPoint) | Supports recovery of Office documents (Word, Excel, PowerPoint) | Supports recovery of Office documents (Word, Excel, PowerPoint) |

How To Recover Data From System NTFS Partition in 2020 With Hetman NTFS Recovery Software 📁🔥⚕️
This article describes the methods of recovering protected and encrypted files. The next article explains the process of recovering files and folders compressed using standard NTSF means.




Yes, there are several alternatives to NTFS file system that may provide better data recovery options. These include: